Ashley Madison Hack: Lessons for Any Business
Regardless what business you're in, someone may dislike you enough to try to destroy you. That's what happened to Ashley Madison. I am not going to weigh in on the moral issues associated with this story. I know what Ashley Madison did for a living, but I want to set that aside for this discussion.
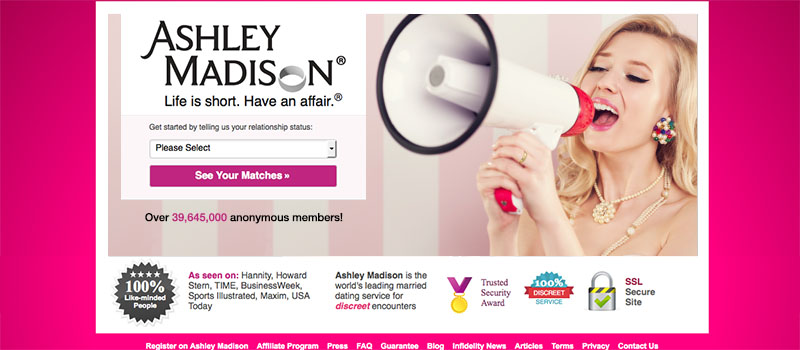
Ashley Madison was selling something, and it may not be what you are thinking. Their one and only product was discretion. The word "discreet" appeared multiple times on their home page. The reason Ashley Madison will go from a company with $120M in annual revenue to less than nothing is because they did not protect their one product, discretion.
What would I have done differently? I couldn't possibly lay out a complete security plan. I don't know enough about what they did do or didn't do to secure their operation. However, we have learned a few things since the hack became public. This exchange is from an email interview between the tech blog Motherboard and the hackers.
Motherboard: "What was their security like?
Hackers: "Bad. Nobody was watching. No security. Only thing was segmented network. You could use Pass1234 from the internet to VPN to root on all servers." Read the entire interview.
Joel Eriksson, CTO of Cycura (an investigator of the Ashley Madison hack), has said “there is no indication of any software vulnerability being exploited during this incident.”
If these two statements prove to be true, then we can make some assumptions about how this hack happened. I say "If" because the hackers may not be telling the truth. It appears that their motivation is to embarrass Ashley Madison, and making it look like their security was sloppy is another way to do that. So, it appears that the hackers did not insert anything in the applications that Ashley Madison used to run their business. They got to the data because the hosting environment was not sufficiently secured.
Of course there may have been things that Ashley Madison could have done better. For example, the hackers say they reached the data via a direct path to the server. That sounds like none of the data was encrypted or the encryption keys were easily found. It also appears that the server access was possible because of a weak password on the server itself. If either is true, for a company that sells discretion, this would be a fail. But let's step back from that level of detail about the case to find some lessons for all businesses.
Your Level of Security Should be Appropriate for Your Risk
Securing data is no different than securing physical property. You do as much as it takes based on the value of what you are protecting. If you sell buckets of mud for a living, you might have a fence around your warehouse just to keep them darn hooligans from throwin rocks at yer winders. If your business is diamonds, and on any given day you may have hundreds of millions of dollars worth of stones, you have redundant security monitor systems, armed guards with attack dogs, bomb-proof vaults, and much more.
So how do you know if your data is secure enough? Start by asking that question often. Things change. A security measure may have been effective when it was installed, but more recently was exploited. Your areas of risk may also have changed.
Just Because You Have Security Measures Doesn't Mean They Are the Right Ones
Ok, I will now attempt to be the first person to compare the Ashley Madison hack to the story of the 9-year-old boy in Taiwan who recently stuck his hand through a 350-year-old painting worth over a million dollars. Here goes. Watch the video. The boy trips over the grossly inadequate barricade placed in front of the painting. The very thing that was supposed to protect the painting was the cause of the accident. Bang! A fist-sized hole.
Ashley Madison apparently had a secure application behind their website. They had a C-level executive with technical staff responsible for security. While they were all watching the door, someone crawled in an unlocked window. The application was secure, but no one was watching the server.
How do you choose which data security measures are right for you? Look at your situation from a variety of perspectives. Do you have customer data? Where does it live? Who is responsible? Would it damage your business or reputation if the data you hold were made public or if it were altered or even destroyed? What do your vendors expect you to do with information they provide you?
As Much As It Takes
That's the answer. The question is: how much effort should I expend to secure my company. Ashley Madison made $120M last year. If they spent $1M last year on security, it wasn't enough. If they spent $50M last year on security, it wasn't enough. Few companies have as much riding on data security as Ashley Madison did, but if data insecurity could put your business at risk, invest in your business' future. If you don't, you may not have a future.
If you have concerns about data security, let's talk. We can help develop an appropriate security plan for your business. Contact us today.
Recent Articles
Look for Opportunities to Change
How you do business may no longer be competitive.
Q&A About Responsive Design
A well thought out discussion with one of our amazing clients.
Ashley Madison Hack: Lessons for Any Business
Security isn't an expense, it's an investment.
SSL is Dead. Long Live TLS.
Dialogs is no longer running SSL for web hosting. Learn how that may affect your company.
Happy 20th Anniversary!
A lot has happened on the internet in 20 years. We have seen it all.
It’s Time to Sell The Studebaker
Over time, many products don’t just change, they get better.
The Couch is Your Enemy: 5 Work-At-Home Pitfalls
Don't let kitten pics and comfortable furniture ruin your productivity.
What You Know Has Real Value.
Is your expertise marketable? Leverage it!
Stay Fit at Your Desk Job: Stand and Walk!
Working a computer job doesn't have to mean living a lethargic life.
Why Javascript?
Keeping up with current technology is not such a bad thing.
Our customers say it best
I continue to be amazed with Dialogs as a product and with the deep technical wisdom of the Dialogs consultants.
— Alex W.